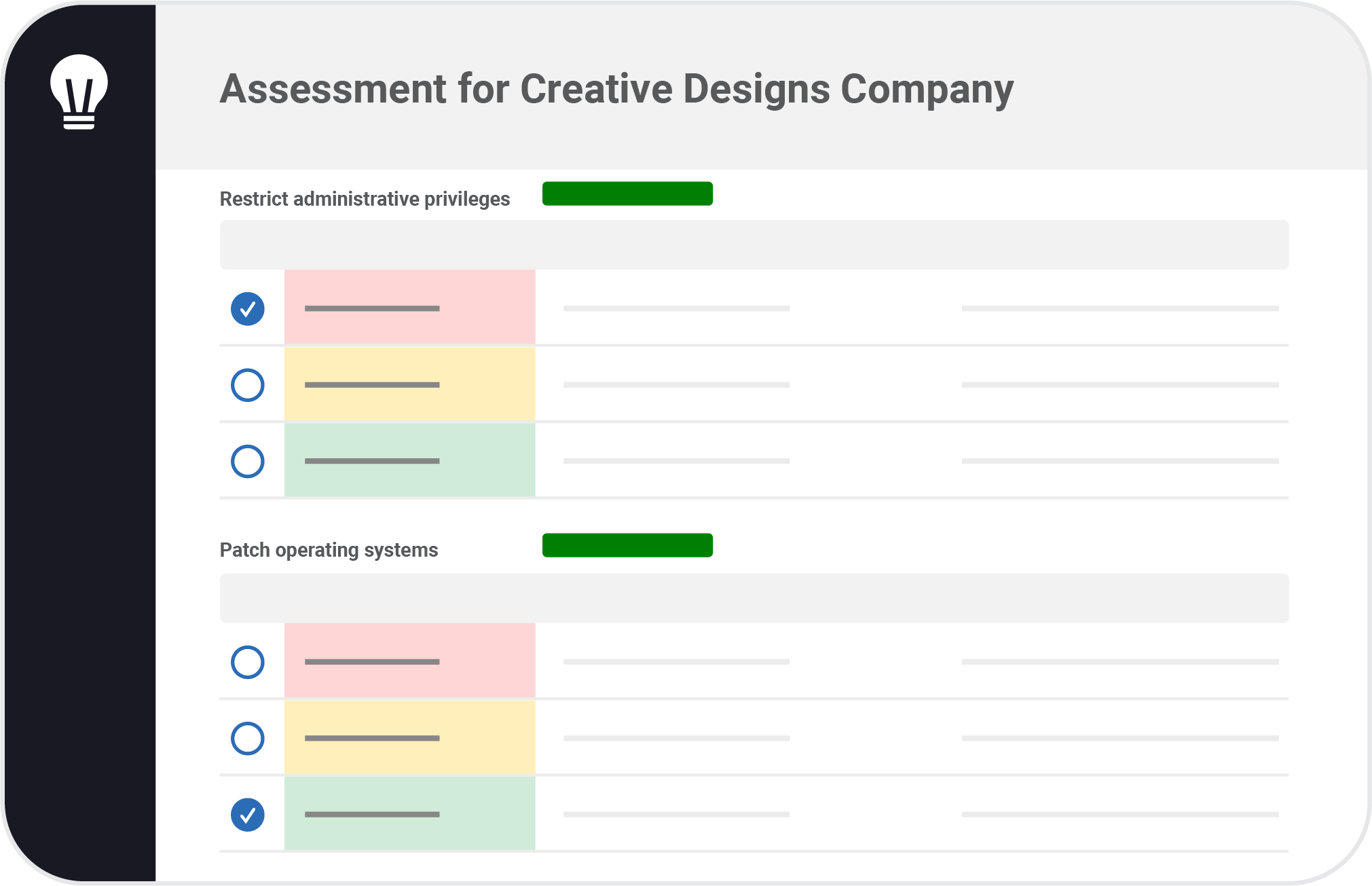
Give clients customized assessments that show how your MSP can help them meet their IT goals and standards. Evaluate their IT environments and track progress over time with pre-built or custom risk assessment templates.
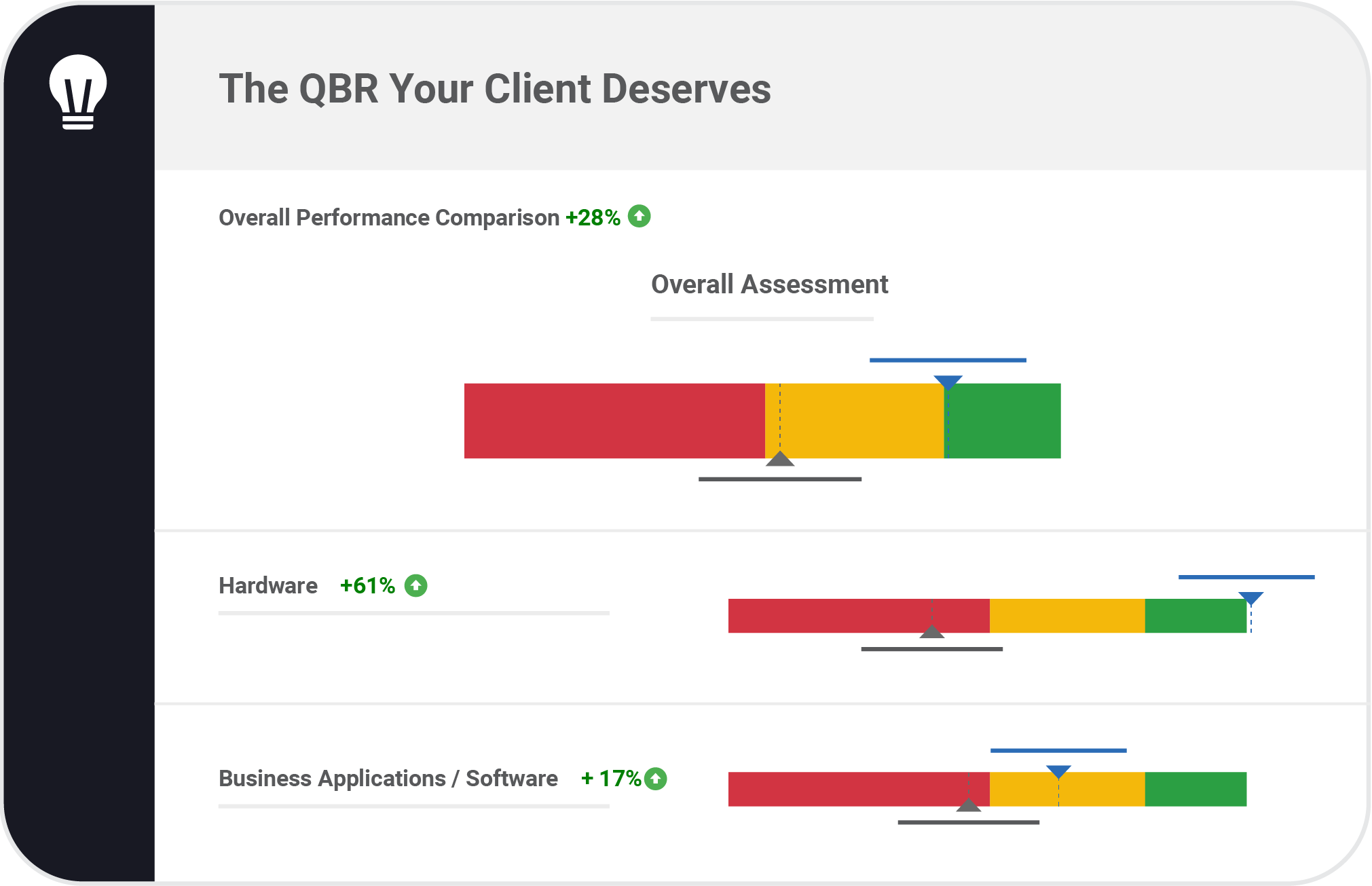
Quickly generate executive-friendly reports that help you deliver the QBR your clients deserve. Create forecast budgets that account for warranty and asset replacement policies and include the total cost of ownership.
Once you identify the problems affecting your clients’ environments, create projects to solve them. Track the progress of each project and communicate with your clients throughout the process.
Strengthen your partnership with clients by showing them the results of your improvements. When they see the value of the investments you suggest, they’ll also see the greater value of your services.
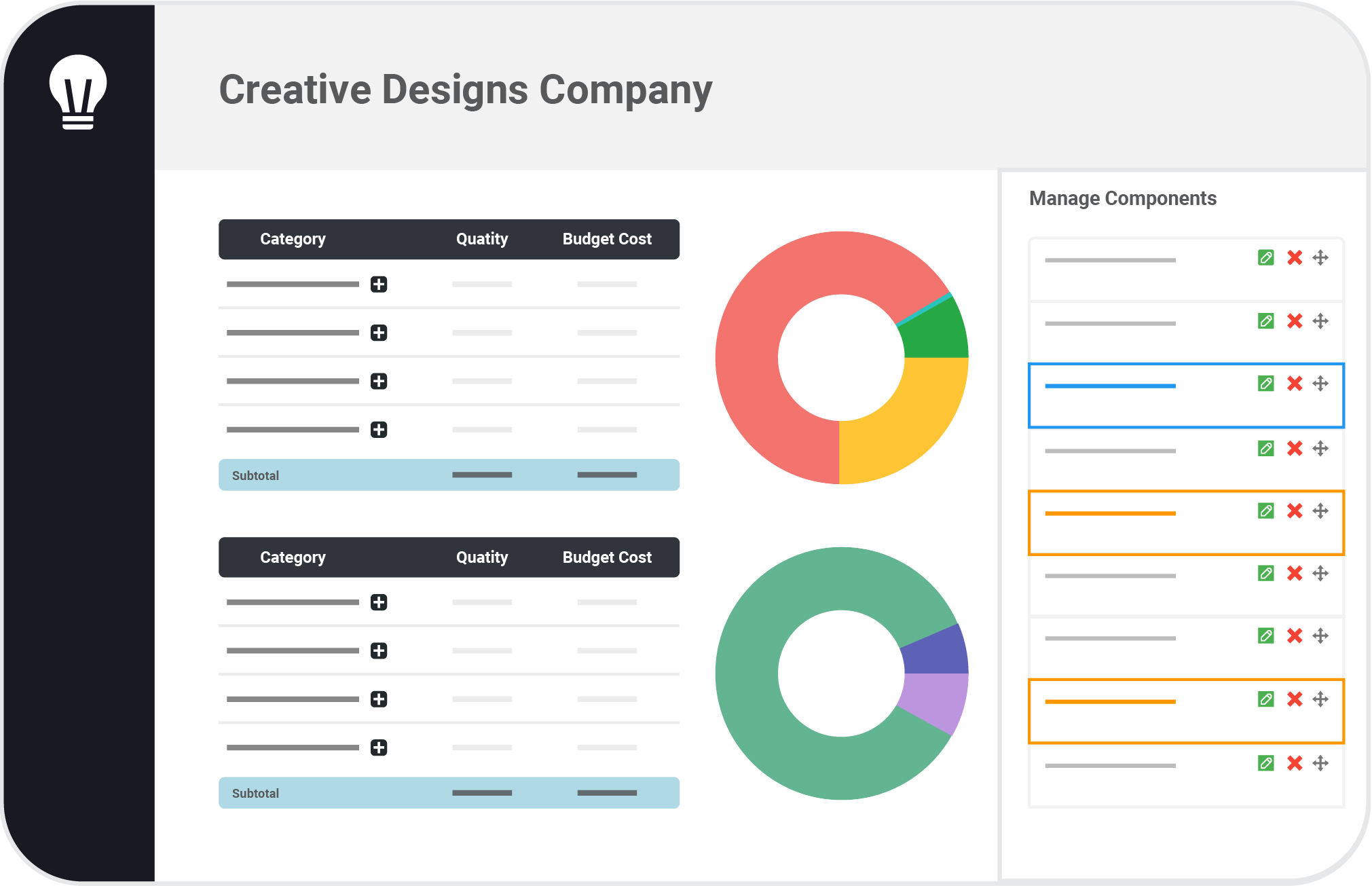

Go from problem-fixer to goal-getter by offering strategic vCIO services to your clients. Help them plan and optimize IT spending by forecasting budgets, cost-savings, and the best investments for long-term success.
Connect with any of our integrations to enhance your vCIO services. Report with real-time data from RMMs, PSAs, and other tools your MSP uses.